 Windows Security Log Event ID 4656
Windows Security Log Event ID 4656

4656: A handle to an object was requested
On this page
This event is logged by multiple subcategories as indicated above.
When you enable auditing on an object (e.g. file or folder), this is the first event recorded when an application attempts to access the object in such a way that matches the audit policy defined for that object in terms of who is requesting the access and what type of access is being requested. (it appears that two subcategories must be enabled, Handle Manipulation and one other such as File System or Registry depending on what type of object you are auditing.)
This event will be Audit Success or Audit Failure depending on whether the user account under which the account is running has the requested permissions or not.
This event's sub category will vary depending on type of object. In the example above notepad.exe running as Administrator successfully opened "New Text Document.txt" for Read access.
This event does not always mean any access successfully requested was actually exercised - just that it was successfully obtained (if the event is Audit Success of course). To determine if any of the permissions requested were actually exercised look forward in the log for 4663 with the same Handle ID.
Win2012 adds 2 new fields: Resource Attributes and Access Reasons.
Free Security Log Resources by Randy
Subject:
The user and logon session that performed the action.
- Security ID: The SID of the account.
- Account Name: The account logon name.
- Account Domain: The domain or - in the case of local accounts - computer name.
- Logon ID: is a semi-unique (unique between reboots) number that identifies the logon session. Logon ID allows you to correlate backwards to the logon event (4624) as well as with other events logged during the same logon session.
Object:
This is the object upon whom the action was attempted.
- Object Server: always "Security"
- Object Type: "File" for file or folder but can be other types of objects such as Key, SAM, SERVICE OBJECT, etc.
- Object Name: The name of the object being accessed
- Handle ID: is a semi-unique (unique between reboots) number that identifies all subsequent audited events while the object is open. Handle ID allows you to correlate to other events logged (Open 4656, Access 4663, Close 4658)
- Resource Attributes: (Win2012) Resource attributes a new feature that allows you to classify objects according to any number of things like project, compliance, security level. It's part of dynamic access control new to Win2012. See this webinar http://www.ultimatewindowssecurity.com/webinars/register.aspx?id=209 See the Win2012 example below. Also more information in this blog http://www.ultimatewindowssecurity.com/blog/default.aspx?p=5aea7883-80c4-40cb-b182-01240cc86070
Process Information:
- Process Name: identifies the program executable that accessed the object.
- Process ID: is the process ID specified when the executable started as logged in 4688.
Access Request Information:
- Transaction ID: unknown.
- Accesses: These are permissions requested. The correspond to the permissions available in the Permission Entry dialog for any access control entry on the object.
- Access Reasons: (Win2012) This lists each permission granted and the reason behind - usually the relevant access control entry (in SDDL format).
- Access Mask: this is the bitwise equivalent of Accesses:
- Privileges Used For Access Check: Lists any privileges requested. The only time I'm aware of this field being filled in is when you take ownership of an object in which case you'll see SeTakeOwnershipPrivilege.
- Restricted SID Count: unknown. Start a discussion below if you have information on this field!
Supercharger Free Edition
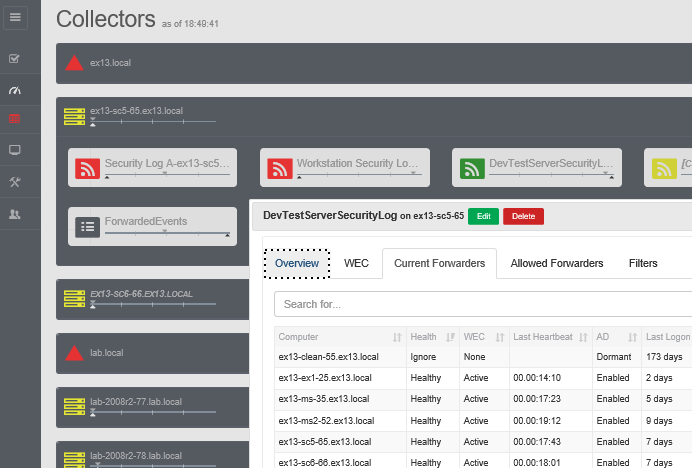
Your entire Windows Event Collection environment on a single pane of glass.
Free.
Win2008 examples
File example:
A handle to an object was requested.
Subject:
Security ID: WIN-R9H529RIO4Y\Administrator
Account Name: Administrator
Account Domain: WIN-R9H529RIO4Y
Logon ID: 0x1fd23
Object:
Object Server: Security
Object Type: File
Object Name: C:\Users\Administrator\testfolder\New Text Document.txt
Handle ID: 0xb8
Process Information:
Process ID: 0xed0
Process Name: C:\Windows\System32\notepad.exe
Access Request Information:
Transaction ID: {00000000-0000-0000-0000-000000000000}
Accesses: READ_CONTROL
SYNCHRONIZE
ReadData (or ListDirectory)
ReadEA
ReadAttributes Access Mask: 0x120089
Privileges Used for Access Check: -
Restricted SID Count: 0
Registry Key Example:
A handle to an object was requested.
Subject:
Security ID: ACME\administrator
Account Name: administrator
Account Domain: ACME
Logon ID: 0x176293
Object:
Object Server: Security
Object Type: Key
Object Name: \REGISTRY\MACHINE\SOFTWARE\MTG
Handle ID: 0x124
Process Information:
Process ID: 0x8d4
Process Name: C:\Windows\regedit.exe
Access Request Information:
Transaction ID: {00000000-0000-0000-0000-000000000000}
Accesses: DELETE
READ_CONTROL
WRITE_DAC
WRITE_OWNER
Query key value
Set key value
Create sub-key
Enumerate sub-keys
Notify about changes to keys
Create Link
Access Mask: 0xf003f
Privileges Used for Access Check: -
Restricted SID Count: 0
Win2012 example
A handle to an object was requested.
Subject:
Security ID: LB\administrator
Account Name: administrator
Account Domain: LB
Logon ID: 0x3DE02
Object:
Object Server: Security
Object Type: File
Object Name: C:\asdf\New Text Document.txt
Handle ID: 0x178
Resource Attributes: S:AI(RA;ID;;;;WD;("Project_MS",TS,0x10020,"Transmogrifier"))
Process ID: 0x113c
Process Name: C:\Windows\System32\notepad.exe
Access Request Information:
Transaction ID: {00000000-0000-0000-0000-000000000000}
Accesses: READ_CONTROL
SYNCHRONIZE
ReadData (or ListDirectory)
WriteData (or AddFile)
AppendData (or AddSubdirectory or CreatePipeInstance)
ReadEA
WriteEA
ReadAttributes
WriteAttributes
Access Reasons:
READ_CONTROL: Granted by Ownership
SYNCHRONIZE: Granted by D:(A;ID;FA;;;BA)
ReadData (or ListDirectory): Granted by D:(A;ID;FA;;;BA)
WriteData (or AddFile): Granted by D:(A;ID;FA;;;BA)
AppendData (or AddSubdirectory or CreatePipeInstance): Granted by D: (A;ID;FA;;;BA)
ReadEA: Granted by D:(A;ID;FA;;;BA)
WriteEA: Granted by D:(A;ID;FA;;;BA)
ReadAttributes: Granted by D:(A;ID;FA;;;BA)
WriteAttributes: Granted by D:(A;ID;FA;;;BA)
Access Mask: 0x12019F
Privileges Used for Access Check: -
Restricted SID Count: 0
Top 10 Windows Security Events to Monitor
Free Tool for Windows Event Collection