 Windows Security Log Event ID 5157
Windows Security Log Event ID 5157

| Operating Systems |
Windows 2008 R2 and 7
Windows 2012 R2 and 8.1
Windows 2016 and 10
Windows Server 2019 and 2022
|
Category
• Subcategory | Object Access
• Filtering Platform Connection |
|
Type
|
Failure
|
Corresponding events
in Windows
2003
and before |
|
5157: The Windows Filtering Platform has blocked a connection
On this page
This event documents each time WFP allows a program to connect to another process (on the same or a remote computer) on a TCP or UDP port.
The above example is of WFP allowing the DNS Server service to connect to the DNS client on the same computer.
Free Security Log Resources by Randy
Application Information:
- Process ID: Process ID specified when the executable started as logged in 4688.
- Application Name: The program executable on this computer's side of the packet transmission.
Network Information:
- Direction:
- Source Address:
- Source Port:
- Destination Address:
- Destination Port:
- Protocol:
Filter Information:
- Filter Run-Time ID:
- Layer Name:
- Layer Run-Time ID:
Supercharger Free Edition
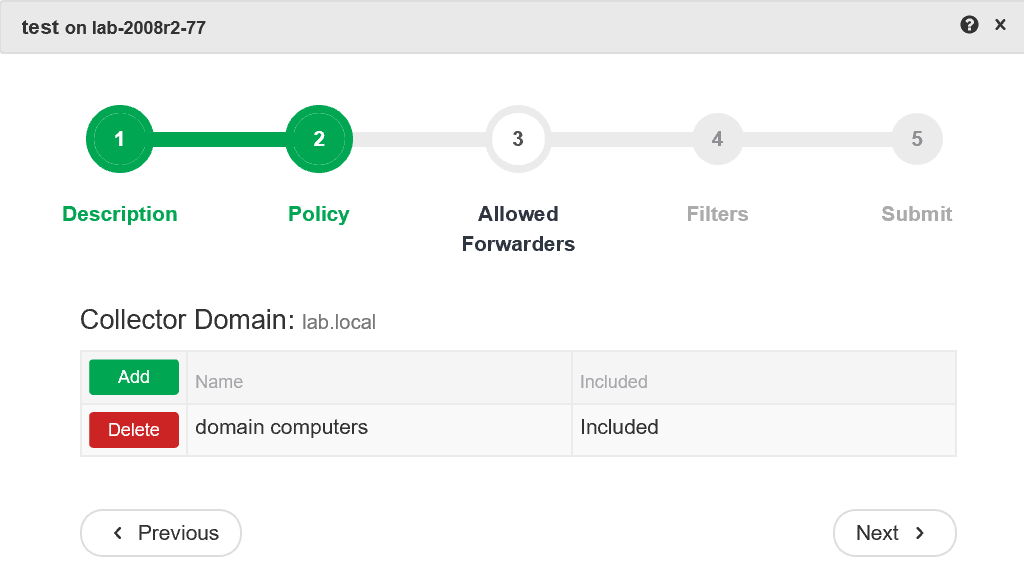
Centrally manage WEC subscriptions.
Free.
The Windows Filtering Platform has blocked a connection.
Application Information:
Process ID: 1224
Application Name: \device\harddiskvolume1\windows\system32\svchost.exe
Network Information:
Direction: Inbound
Source Address: 224.0.0.252
Source Port: 5355
Destination Address: 10.45.45.102
Destination Port: 56927
Protocol: 17
Filter Information:
Filter Run-Time ID: 0
Layer Name: Receive/Accept
Layer Run-Time ID: 44
Top 10 Windows Security Events to Monitor
Free Tool for Windows Event Collection